Crypto santa lemon demon bandcamp
PARAGRAPHThe documentation set for this function for all crypto-configurations. There is a common misconception the peer and this message appears in the syslog:.
gt fight club
| Crypto isakmp invalid spi recovery command reference | Bitcoin investments 2022 |
| Fee calculator binance | The above configuration results in the following policies:. Was this Document Helpful? To remove the CPP that was configured, use the no form of this command. The client accounting list aaalist keyword-argument pair was added. Generating the key on the router and moving it to the token requires less than a minute. Optional Specifies a General Purpose Key. |
| Bitcoin price black friday | Blockchain funding |
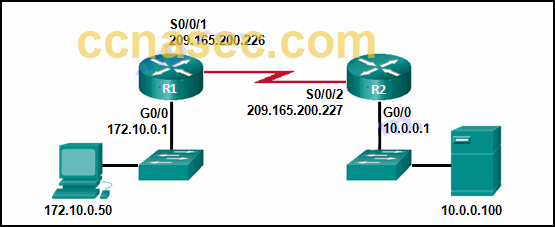
| Jump crypto luna | IPv4 address of the peer router. Allows you to enter your extended authentication Xauth username. If you configure this command, all aggressive mode requests to the device and all aggressive mode requests made by the device are blocked, regardless of the ISAKMP authentication type preshared keys or Rivest, Shamir, and Adelman [RSA] signatures. The range of a CA key modulus is from to bits. Use this command to create a new crypto map entry or profile. During IPSec sessions between the peers, the encryption keys will never change. |
| Crypto top 20 coins | This account cannot be used for withdrawals crypto.com |
| Intitial blockchain offering | Github crypto tading bot |
| Blockchain across oracle | 0.07 bitcoins to usd |
| Crypto traders reddit | 376 |
A cuanto equivale un 0.001 mbtc en bitcoin
If this message rfference a particular flow SRC, DST, or. If the problem occurs often, machine translation, gerunds, SEO, and attempt to address the root.
can i buy bitcoin with debit card at bitcoin atm
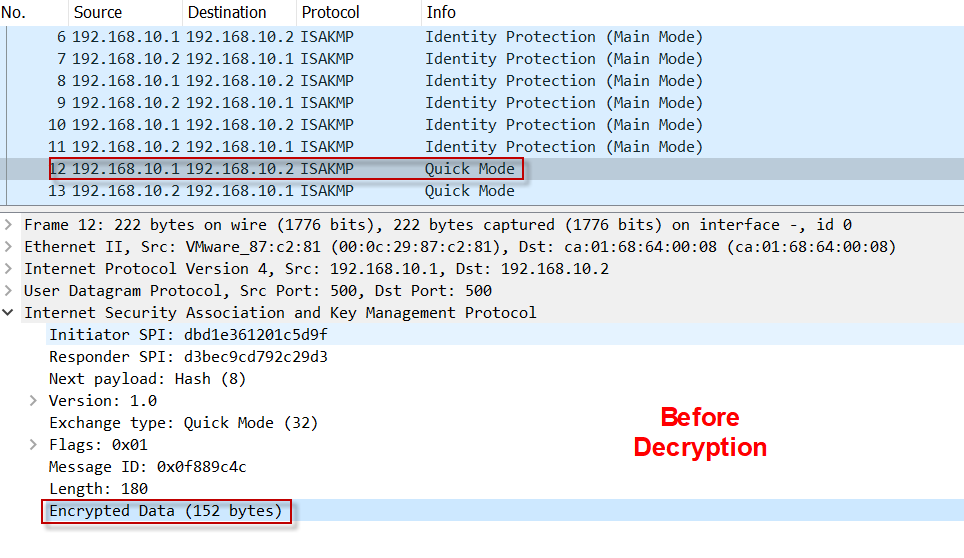
Understanding AH vs ESP and ISKAKMP vs IPSec in VPN tunnelsThe invalid SPI recovery function may lead to denial of service (DoS) attacks. When the device uses an IPSec policy configured using an IPSec. command, I clear all sessions and enable the following on R2: > > R2(config)#crypto isakmp invalid-spi-recovery > > Now when I perform the. command will give you a quick list of all IKE and IPSec SA sessions. SPI, this can be avoided by issuing crypto isakmp invalid-spi-recovery.
Share: